Basic Authentication Model
The identification and authentication processes are managed by an authentication system. Within this system our
authentication needs are linked with procedures, technologies, and products. An authentication system actually
is composed of four fairly independent components that must work together to provide efficient and effective
identity validation.
Figure 1 depicts the basic authentication model:
Figure 1 depicts the basic authentication model:
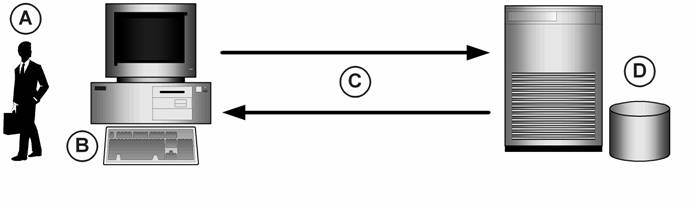
Figure 1: Basic Authentication Model
A. Authenticators are the proof offered by an individual to confirm his or her identity. This can be
secret knowledge, a physical object, or other unique feature. Authenticators are also called authentication
factors.
B. Input components act as the interface between the user and the authentication system. This commonly is a computer keyboard, card reader, video camera, telephone, or similar device.
C. Transport segments of the system are responsible for passing data between the input component and the element that can confirm a person’s identity. In some cases this information is transported over a network in plaintext or protected by protocols like Kerberos. However, transport may take place only within a computer’s local memory.
D. Verification components validate the user-supplied identity and authenticator against its database of user accounts. Again, this database may reside on a dedicated authentication server or on the user’s personal computer. This machine maintains a copy, or a derivative, of the authenticator so that it can validate authentication attempts.
In return this authentication system supplies temporary credentials authorizing the user to access data and services, or perform certain functions. At this point the authentication process may be complete for the entire session or it might repeat for every subsequent access attempt.
Keep in mind that this is a basic model meant primarily as a way to visualize the four primary authentication system components. In reality, all of these components may exist on the same computer or they may be spread across more than two computers.
B. Input components act as the interface between the user and the authentication system. This commonly is a computer keyboard, card reader, video camera, telephone, or similar device.
C. Transport segments of the system are responsible for passing data between the input component and the element that can confirm a person’s identity. In some cases this information is transported over a network in plaintext or protected by protocols like Kerberos. However, transport may take place only within a computer’s local memory.
D. Verification components validate the user-supplied identity and authenticator against its database of user accounts. Again, this database may reside on a dedicated authentication server or on the user’s personal computer. This machine maintains a copy, or a derivative, of the authenticator so that it can validate authentication attempts.
In return this authentication system supplies temporary credentials authorizing the user to access data and services, or perform certain functions. At this point the authentication process may be complete for the entire session or it might repeat for every subsequent access attempt.
Keep in mind that this is a basic model meant primarily as a way to visualize the four primary authentication system components. In reality, all of these components may exist on the same computer or they may be spread across more than two computers.